How WRAP Works - An Analogy
You can think of a WRAP cookie like a high school hall pass. You cannot roam the halls without your hall pass. Once you get a hall pass, you can get around the school as you like, until the pass expires.
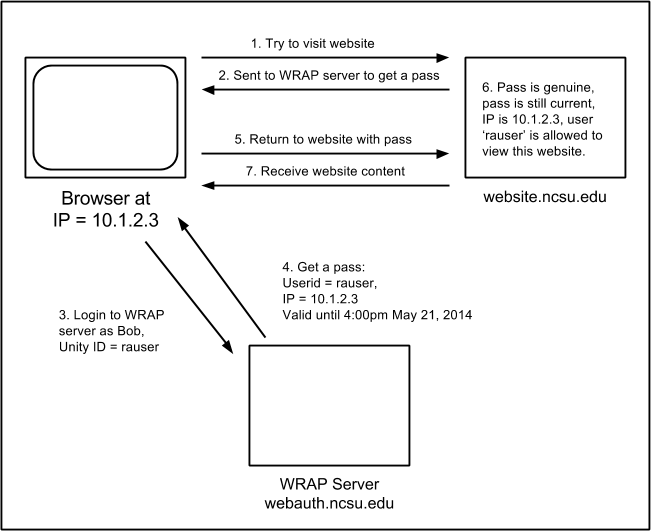
Getting a Pass
You open your browser and visit an ncsu.edu website. Many of those websites don't require a WRAP pass (which is really a browser cookie), so they just let you in.
When you visit an ncsu.edu website that does require a WRAP pass, it will check to see if you showed them your pass when you came in. If you didn't, it sends you to the WRAP server (the office) to get a pass.
The WRAP server checks your login and password to verify your identity. It then issues you a WRAP pass, which reads: "this is Bob (really your Unity ID), who is visiting from this IP address, and this pass expires at this time and date." WRAP uses Public-key cryptography to protect the pass so the website can ensure the pass is genuine, and not forged.
The WRAP server then sends you back to the original site. When you arrive there, you show your pass at the door. The site checks the pass to make sure
- it was generated by the WRAP server,
- it is still valid for the current time, and
- you are connecting from the IP address in the pass.
If any of these checks fail, you will be sent back to the WRAP server for a new pass.
Wandering the Halls with a Pass
- Once you have a WRAP pass, your browser will show it at every website ending in ncsu.edu, but only those websites and no others. Your browser will show your pass whether the website requires the pass or not.
Trying to Remove a Pass
When you close your browser, it will automatically forget your copy of the pass.
When you visit the WRAP server to logout, it will replace your copy of the pass with a note that says, roughly, "this is not a valid pass anymore."
Just because you've forgotten your pass, doesn't make the pass invalid. You've been showing the pass to every ncsu.edu website that you visit. Any of them could have made a copy of your pass, and could try to use it to impersonate you. WRAP has no way to invalidate an issued pass before the expiration time. This is why the IP address is encoded on the pass. It makes it harder for someone with a different IP address to impersonate you.
Shared and Proxied IP Addresses
Many people run their own local networks at home, or visit coffee houses or other public Wifi access points that can share one public IP address. Someone sharing one of these networks with you could easily use your pass to impersonate you if they get a copy of it.
Some networks send your browser through a proxy server to connect to websites on the internet. When you visit an ncsu.edu website through one of these proxies, your connection be from the IP address of the proxy and that is what will be written on your pass. Because of this, any users going through the same proxy could easily use your pass to impersonate you if they get a copy of it.
In some networks, you might be connecting through one of several proxies acting together, all with different IP addresses. Your pass will have written on it the IP address of the proxy you used to connect to the WRAP server. When your proxy is changed, it will not match the IP address of the last proxy you used to connect to a particular ncsu.edu website. Then, your pass will be rejected, and you'll be directed to get a new one.
To help with the multiple proxy problem, WRAP offers a special "1 hour, any address" pass. This pass says, roughly, "This is Bob, do not check the IP address on the pass."
If you have an "any address" pass, anyone who can get a copy of that pass can use your pass to impersonate you, for up to an hour, from anywhere.
Solving WRAP's Issues
These issues were considered when WRAP was designed, more than 14 years ago. At the time there was no better solution available, and these risks were considered to be small and acceptable.
We will probably turn off the option for "any address" pass in the near future, because they are so easily used to impersonate you. This will break WRAP for people whose IP address changes frequently, either from multi-proxy networks, or from some wireless providers.
This will not solve the other problems with WRAP:
- An IP address does not uniquely identify an individual. They are often shared, and can be re-used later by another person.
- Weaknesses in Web 2.0 scripting can make it easy to capture the WRAP pass from another user.
- WRAP has no way to invalidate a pass after it has been issued, prior to the expiration time.
- Your browser gives out your WRAP pass to every ncsu.edu website.
- WRAP is a homegrown, non-standard web authentication mechanism. It is not compatible with systems anywhere else.
Rather than devote the time and resources to try to fix WRAP, we will be moving our web authentication services to Shibboleth, which does not suffer from these design problems.

